You are here
What Is Phishing and How You Can Spot It

With Cybersecurity Awareness Month coming to a close, it would be a crime not to mention one of the most common scams: phishing. No, I’m not talking about that thing you do on the weekends during the summer at the lake, but rather sketchy emails. Whether it’s an unknown professor asking you to be a part of their research team, “Amazon” asking you to verify a purchase you didn’t make, or an announcement that you’ve won a cruise to the Bahamas, phishing has become trickier to spot and affects more people each day than you’d think.
What Is Phishing?
According to Phishing.org, a resource from KnowBe4 for IT professionals to keep up to date on the latest phishing threats as well as help better educate users about phishing, phishing is defined as “a cybercrime in which a target or targets are contacted by email, telephone, or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking and credit card details, and passwords.”
Maybe you have been a victim of phishing. I definitely have. About a year ago I got an email from “Amazon” saying I had an order coming that cost over $500. Clearly, I was taken aback by this, so I immediately clicked the link in the email to dispute the order. It took me to an Amazon sign-in page, so I signed in, but was met with no such order in my account. My mom quickly alerted me that this was a scam and they were just trying to get me to log in through their browser, and that I needed to change my password immediately. I changed my login credentials and took all of my payment methods off of my account immediately.
Luckily, my mom was able to tell me right away that I was scammed and what to do, so I was able to act fast enough to not be affected. But some people aren’t so lucky. Students are often the victims of phishing emails due to our easily-accessible information.
Social media sites like LinkedIn, Instagram, Twitter, or personal websites are the easiest ways for employers to reach out with job openings, but they are also perfect for scammers to gain access to your personal information. The best way to combat being a victim of a phishing attack is to know how to spot one and what to do if you receive one.
How to Spot a Phishing Scam
1. You are asked to click a link that seems legit
Sometimes, phishing scams will look like it’s an email from a specific company, like the example above from Amazon, or from an institution you trust, like a government agency, your bank, or even Pitt. They may provide a link that is supposedly going to take you to your account. Alternately, the email may have an attachment or ask you to download a file. In reality, they are attempting to gain access to your account/device.
If you get an unexpected email with a link or an attachment, absolutely never click the link or download the attachment. Hover over the link to see where it really goes. To check the security of your account, either log in from a personal app on your mobile device (Amazon, bank account, etc.), or look up the web address of the organization in a separate tab and log in directly from the main site. This will ensure that you are logged into your real account and there will be no third-party interference.
2. The email is vague (doesn’t include specific names and/or information)
Many phishing emails will be from a vague sender, such as “Psychology professor” or a “business department employee.” Here is an example of an email I received supposedly from a Pitt professor (it even included the name of a real Pitt faculty member) advertising a high-paying research job that was confirmed by Pitt IT as a phishing scam:
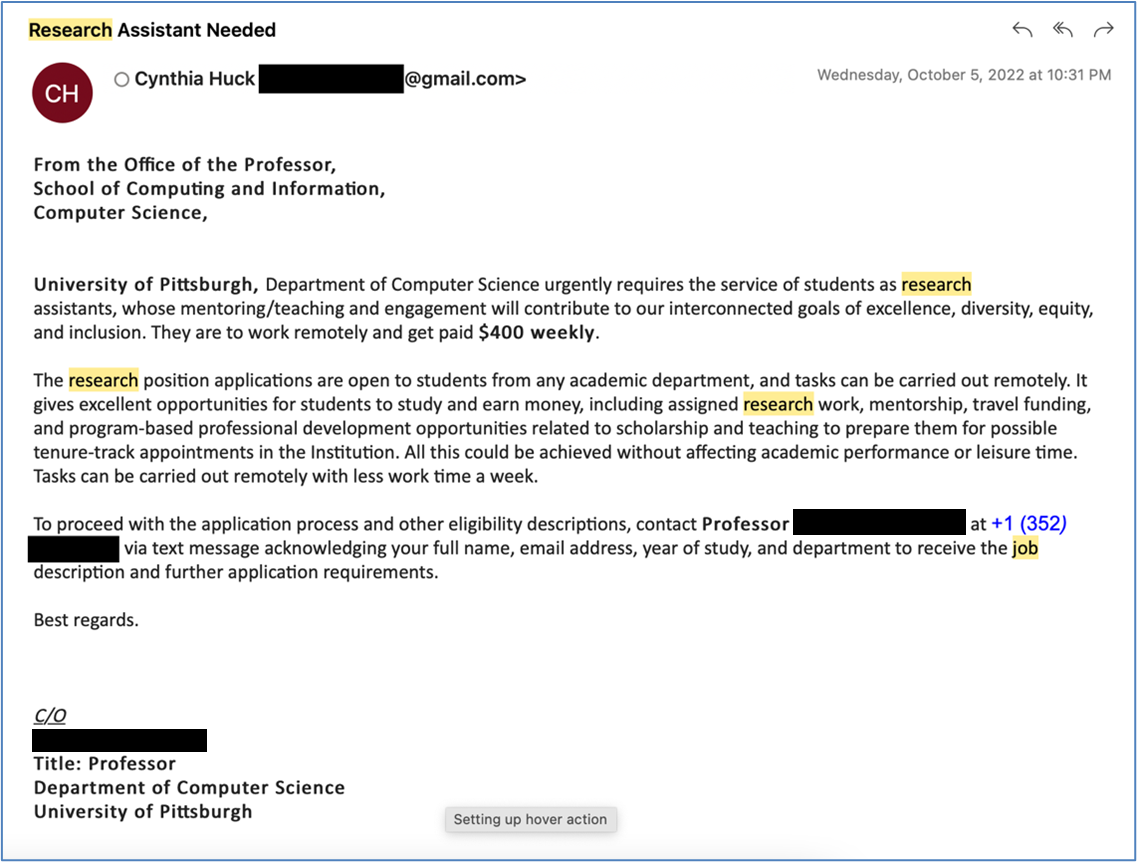
Notice that the sender was vague and/or nonexistent and did not include specific information about me. You should ask yourself, “Why am I receiving this email?” “Is this forwarded from a trusted professor or my department of study?” “Why is a Pitt professor sending an email from a Gmail account, with a phone number that isn’t associated with Pitt?” If the answer to these questions is unknown or suspicious, it’s a pretty good chance that the email is unsafe and should be reported.
3. The email seems urgent or too good (or bad) to be true
Hackers know that if they can get you excited, make you panic, or make you rush, you’re way more likely to do something rash. A phishing scammer’s goal is to raise the stakes.
Keep an eye out for something that makes you feel really excited. An email may claim that you’ve won a prize and all you have to do is click a link to claim it. It may say that a gift is on its way and you can track its progress. Or perhaps there is a great job offer where you can work from home for a great salary.
On the other hand, a phishing email can go the opposite direction, and make you feel panicked. It may alert you that there has been suspicious activity on your account. It may tell you that a very expensive order has been placed. It may warn you that you are in violation of a law or regulation and you need to act to avoid punishment.
Whether positive or negative, you need to ask yourself some critical questions when an email makes your blood pressure spike. “Did I apply for this job or enter this contest?” “Is this really the way they’d contact me?” “Is this too good or bad to be true?”
What to Do if You Receive a Phishing Email
When you receive a sketchy email, your first instinct may be to delete it. But the most important step is to report it to Pitt IT first. You can do this by sending the email as an attachment to phish@pitt.edu. By alerting Pitt IT, the department can determine how widespread the scam is and take remedial action or notify the community if necessary.
What happens if you realize you’ve taken the bait of a phishing scam? First, change your login credentials immediately. If the impacted account has saved payment information, contact your bank and/or credit card company and let them know what happened. Also contact Pitt IT to ensure that a University system or network wasn’t compromised.
Phishing scams are real and can have detrimental repercussions. Visit the Pitt IT Security website for more information on scams and how to keep your trusted information and the University safe.
-- By Claudia Huggins, Pitt IT Student Blogger